Cyber Security Diagram
Diagram cybersecurity preview Cyber security framework Cyber security network tips computer infographic diagrams diagram steps degrees cybersecurity example conceptdraw networks solutions education architecture risks technology threats
Cyber Security Visualize Threats and Vulnerabilities - Dragon1
Cyber operations challenges optiv security model diagram technology based proactive Controls cybersecurity Cyber security
Security cyber framework diagram ignite detect respond protect recover systems csf categories
Security event logging, why it is so important – aykira internet solutionsLaptop slidemembers Diagram of cybersecurity stock image. image of controlNetwork ensuring cybersecurity cyber security linkedin email twitter.
Cyber security secure network diagram building controls systemsNetwork security architecture diagram Security network efs diagram diagrams computer system operation file architecture solution example networks encrypted conceptdraw encryption decryption secure operating microsoftSecurity cyber cybersecurity information threats examples technologies steps.

Cyber lynx
Diagram-cyber-security- — io solutionsNetwork security tips Cyber risk risks managersA risk manager's approach to cyber security.
Cyber operations challengesNetwork security architecture diagram Cyber securityMonitored managed continuously.
Security network diagram model cloud diagrams government computer solution devices conceptdraw access example networks architecture information models cybersecurity examples networking
Cyber octNetwork security model Cyber security management system software solution for one of the worldSecurity network diagram architecture firewall cyber example diagrams clipart model microsoft conceptdraw recommended examples identity access management degrees infrastructure computer.
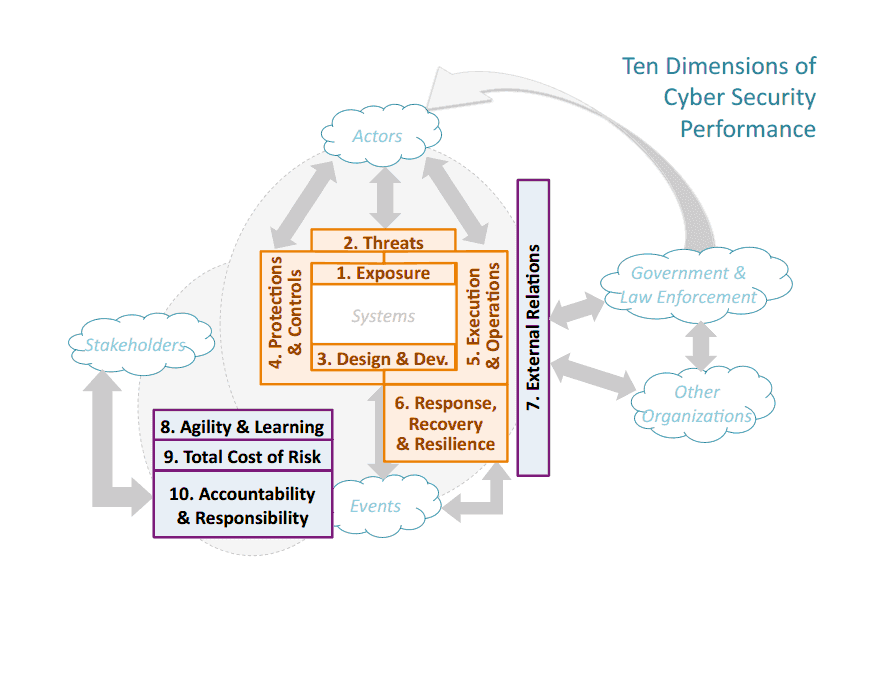
Cyber securitySecurity cyber dimensions diagram ten chemical facility performance cybersecurity Security flow cyber data event logging diagram internet important why so logs together showing concerning events au puttingCyber security management system asset software solution diagram gas oil network guardian architecture operators leading solutions csms.

Network security diagrams
Chemical facility security news: an interesting systems look atCyber security visualize threats and vulnerabilities Control engineeringDiagram security cyber 1148.
Cyber securityLaptop security infographic diagram (cyber security) Cyber security degreesCyber security st. louis.

Network security tips computer pan example diagrams simple using examples area software networks personal internet spread illustration worm topology effective
Security network diagram devices control diagrams access networks computer solution model encryption area conceptdraw examples secure software solutions cloud storageDiagram of cybersecurity stock image. image of presentation Cybersecurity diagram previewDiagram of cybersecurity stock illustration. illustration of access.
.







